As cyber threats continue to grow in scale and sophistication, organizations can no longer rely solely on traditional security audits and internal testing teams. Modern businesses are turning to bug bounty platforms like Bugcrowd to tap into global communities of ethical hackers who proactively identify vulnerabilities before malicious actors can exploit them. These platforms provide structured environments for reporting, validating, and resolving security issues efficiently and at scale.
TLDR: Bug bounty tools like Bugcrowd help organizations manage vulnerabilities by connecting them with ethical hackers worldwide. These platforms streamline vulnerability reporting, triage, and remediation through structured workflows and collaboration features. They improve security posture while reducing risk and response times. Ultimately, they turn external security researchers into valuable partners in cyber defense.
Rather than viewing security as a closed internal function, companies are increasingly embracing crowdsourced security testing. Bug bounty platforms offer purpose-built systems that allow organizations to manage large volumes of vulnerability submissions, prioritize risks, and ensure responsible disclosure without chaos.
What Are Bug Bounty Platforms?
A bug bounty platform is a managed service that connects organizations with independent security researchers. These researchers hunt for vulnerabilities in exchange for financial rewards, recognition, or both. Platforms like Bugcrowd provide structured programs that define scope, rules of engagement, payout models, and disclosure processes.
Unlike informal vulnerability reporting methods, these tools offer:
- Submission portals for standardized vulnerability reports
- Triage systems to validate and prioritize findings
- Reward management systems to handle payouts
- Analytics dashboards for tracking trends and performance
- Communication channels between researchers and organizations
This organized environment ensures that both companies and ethical hackers operate within clear expectations and legal protections.
How Bugcrowd-Like Tools Manage Vulnerabilities
Managing vulnerabilities effectively requires more than simply receiving reports. It involves verification, prioritization, remediation coordination, and long-term tracking. Platforms like Bugcrowd integrate each of these steps into one ecosystem.
1. Vulnerability Submission and Intake
Researchers submit detailed reports that typically include:
- Description of the vulnerability
- Steps to reproduce the issue
- Proof of concept evidence
- Impact assessment
- Suggested remediation guidance
Most platforms standardize this information using templates, significantly reducing incomplete or vague reports.

2. Triage and Validation
One of the largest challenges in vulnerability management is filtering legitimate findings from duplicates or false positives. Bug bounty platforms often provide dedicated triage teams or automated systems that:
- Validate the authenticity of reported issues
- Eliminate duplicate submissions
- Assess severity using industry frameworks like CVSS
- Assign priority levels
This step is critical because large public programs may receive hundreds or even thousands of submissions per month. Proper triage ensures internal security teams are not overwhelmed.
3. Collaboration and Communication
Bug bounty platforms facilitate structured dialogue between researchers and internal development teams. Secure messaging systems allow clarification of technical details without exposing vulnerabilities publicly.
Clear communication prevents misunderstandings and speeds up remediation. Researchers may provide additional testing data, while development teams may request more context or confirmation after applying fixes.
4. Patch Management and Resolution Tracking
After validation, vulnerabilities enter remediation workflows. Many platforms integrate with ticketing systems like Jira or ServiceNow, allowing:
- Automatic ticket creation
- Status tracking from open to resolved
- Internal assignment to appropriate teams
- Verification of successful patches
By connecting directly to development pipelines, bug bounty tools transform vulnerability discovery into actionable development tasks.
5. Rewards and Recognition
Reward management is another critical component. Platforms calculate payouts based on:
- Severity level
- Exploit complexity
- Business impact
- Program budget
Beyond monetary rewards, researchers may gain public recognition via leaderboards and reputation systems, further incentivizing responsible participation.
Key Features of Platforms Like Bugcrowd
While each platform has its own approach, common features include advanced management tools designed to streamline vulnerability lifecycles.
Program Customization
Organizations can configure:
- Scope definitions (domains, applications, APIs)
- Testing guidelines
- Private or public program access
- Reward structures
Private programs often invite a smaller group of vetted researchers, while public programs open participation to a wider community.
Researcher Vetting and Skill Matching
Some platforms assess researchers based on skill levels, past performance, and reputation. This allows companies to match their programs with specialists in:
- Web application security
- Mobile security
- Cloud infrastructure
- IoT systems
- API security
This curated approach increases report quality and reduces noise.
Analytics and Reporting
Data-driven insights help security leaders identify patterns and improve defenses. Dashboards may track:
- Total vulnerabilities discovered
- Average time to remediation
- Severity distribution
- Recurring vulnerability types
- Researcher performance metrics
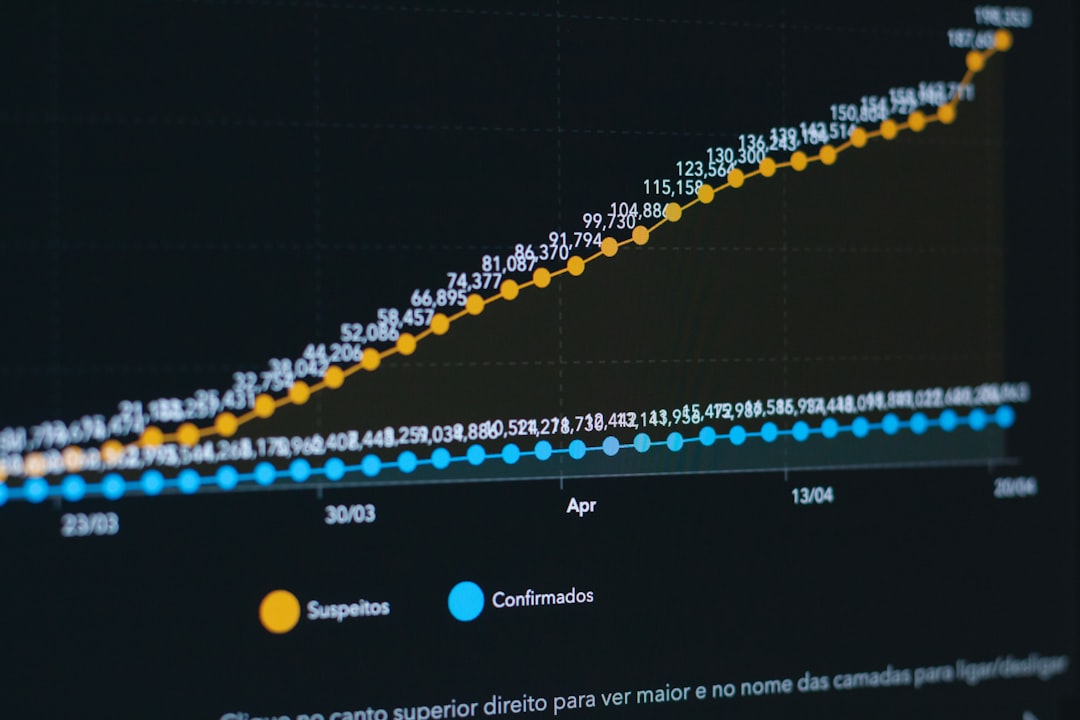
Over time, these insights allow organizations to strengthen their development practices and reduce recurring risks.
Benefits of Using Bug Bounty Tools
Continuous Testing
Unlike one-time penetration tests, bug bounty programs provide ongoing assessment. Ethical hackers test systems continuously, identifying emerging threats as software evolves.
Scalability
Traditional security testing often depends on limited in-house expertise. Bug bounty tools provide access to thousands of global researchers, allowing rapid scaling of testing capacity.
Diverse Skill Sets
Cybersecurity threats vary widely. A crowdsourced approach brings diverse perspectives and creative attack methods that internal teams may overlook.
Cost Efficiency
Organizations pay for validated results, not just effort. Rewards are distributed based on confirmed vulnerabilities, making expenditures closely aligned with actual security improvements.
Responsible Disclosure Framework
Bug bounty platforms provide formalized disclosure channels, reducing the risk of public leaks or adversarial relationships with researchers.
Challenges and Considerations
While powerful, bug bounty platforms require thoughtful implementation.
Volume Management
Without proper triage systems, organizations may struggle with high submission volumes. Partnering with managed services providers or using automated filtering tools helps alleviate this burden.
Clear Scope Definition
Poorly defined scope can lead to confusion, unauthorized testing, or wasted resources. Platforms encourage precise documentation to prevent misunderstandings.
Internal Readiness
Companies must prepare development teams to handle incoming vulnerabilities efficiently. Without strong internal processes, even high-quality reports can stagnate.
Legal and Compliance Factors
Clear legal frameworks protect both researchers and organizations. Proper contracts and safe harbor language are essential components of any program.

Bug Bounty Platforms vs. Traditional Vulnerability Management
Traditional vulnerability management often relies on:
- Internal scanning tools
- Periodic penetration tests
- Employee security reviews
Bug bounty platforms complement these methods rather than replace them. They provide a continuous, adversarial testing perspective that mimics real-world attack scenarios more dynamically.
By integrating bug bounty findings into broader vulnerability management programs, organizations create layered defenses that are more resilient against evolving threats.
The Future of Vulnerability Management Platforms
As cybersecurity technologies evolve, bug bounty tools are becoming smarter and more automated. Future developments may include:
- AI-assisted triage to reduce duplicate reports
- Automated risk scoring enhancements
- Deeper DevSecOps integrations into CI CD pipelines
- Enhanced researcher reputation systems
- Expanded coverage for emerging technologies like AI systems and blockchain
Organizations that embrace these innovations position themselves to respond proactively rather than reactively to cyber threats.
Conclusion
Bug bounty tools like Bugcrowd represent a fundamental shift in how organizations manage vulnerabilities. By harnessing the power of global ethical hacker communities, these platforms provide structured, scalable, and cost-effective solutions for identifying and resolving security flaws.
Through standardized reporting, professional triage, seamless collaboration, and robust analytics, they transform vulnerability management into a continuous improvement process. As cyber risks grow more sophisticated, adopting a crowdsourced security strategy is not merely innovative — it is increasingly essential.
FAQ
1. What is the difference between a bug bounty program and penetration testing?
Penetration testing is typically time-bound and conducted by a specific firm or team. Bug bounty programs are ongoing and involve a broader community of independent researchers who test systems continuously.
2. Are bug bounty platforms suitable for small businesses?
Yes, but smaller organizations may benefit from starting with private programs or vulnerability disclosure programs before launching large public initiatives to manage costs and workload.
3. How are vulnerability rewards determined?
Rewards are generally based on severity, impact, exploitability, and program guidelines. Critical vulnerabilities typically receive higher payouts.
4. Can bug bounty platforms replace internal security teams?
No. They complement internal teams by providing additional external testing perspectives. Internal teams still manage remediation and long-term security strategy.
5. Are submissions confidential?
Yes. Structured bug bounty platforms include secure communication systems and responsible disclosure policies to ensure vulnerabilities are not publicly disclosed before remediation.
6. How long does it take to fix reported vulnerabilities?
Remediation time varies based on severity and organizational readiness. Critical vulnerabilities are usually prioritized and resolved faster than lower-risk issues.



